WARNING: These are scams. They are Emails sent to a honeytrap address only ever used for this purpose. Do not reply to these people, they will try to con you into paying out money in return for nothing.
CAVEAT: Please note that some of these Emails may be impersonating a genuine company or person. We wish to make it clear that any such name mentioned within these Emails has no connection to the scam. For the sake of searching, we leave these messages untouched, but we will respond to any concerns left in our comments.
From: "American Express" <[email protected]>
Date: Mon, 10 Apr 2017 13:50:51 -0700
Subject: Suspicious sign in detected from unknown browser
Dear American Express Customer:
We detected something unusual about a recent sign-in to the American Express.
To help keep you safe, we required an extra security challenge.
If you’re not sure this was you, a malicious user might have your password. Please review your recent activity and we’ll help you take corrective action.
Kindly download the attached file below for your safety.
If you aren’t enrolled in Paperless Statements and think you’ve received this message in error, please call our Customer Support team immediately, using the phone number on the “Contact Us” page on American Express.
If this was you, then you can safely ignore this email.
Please don’t reply directly to this automatically-generated e-mail message.
Sincerely,
(c) 2017 American Express
Technical Analysis
Analysis of the IP addresses contained within the header reveals that the Email has come from the IT systems of efox. Efox is a legitimate company based in China. The domain was originally created in 2008, so they are well established. Their mail servers are appearing on many spam blacklists so it is likely that they unfortunately succumbed to a hacking or are hosting a viral spambot in their system. (At the time of this EMail – April 2017)
It would appear that their [email protected] is the address that has been infiltrated, although it may just be a generic name being used. Note that the sender name appears as “American Express”, which is what most Email clients will display. A handy tip to spot fake Emails is to compare the human readable and the Email address of the sender – a mismatch is a giveaway (Compare “American Express” with “[email protected]” ) – but do not assume a match indicates a good Email.
The Email we received was multipart, the part we do not publish for obvious reasons was an HTML form.
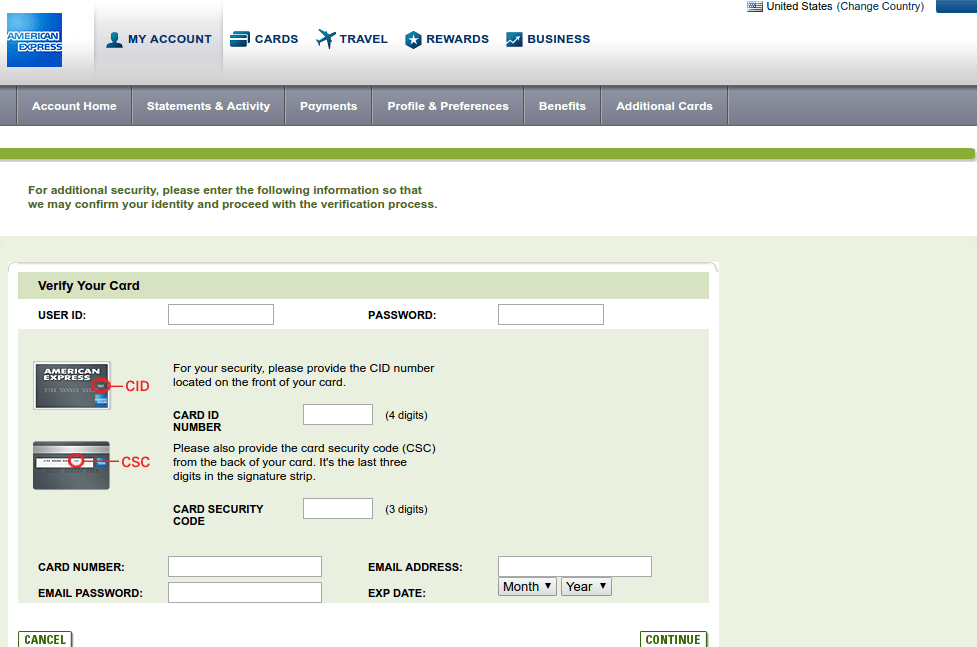
The form is designed to look like its from American Express, even using genuine American Express links to display images and download the CSS files. Instead of posting the form with all your secure details to American Express, the fake form sends the captured data to a Dutch registered domain.
The usual method for a hacker is to place the form processing script onto a breached site, although in this case, it looks like the perpetrator created an account with a hosting company. The domain name was just some random consonants and the domain now shows a “account suspended message”.
Moral of the story: Unless you have actually ordered something from efox-shop.com, any Emails from them are likely to be suspect. Generally, never trust an Email and never click on an Email link. (The only exception is when you request a password reset and the Email arrives seconds later.